Pandora Labs Security Stack
Get to know what makes Pandora Labs the best security company for you.

Get to know what makes Pandora Labs the best security company for you.
















Get to know the best security solution for your IT Infrastructure & your websites.

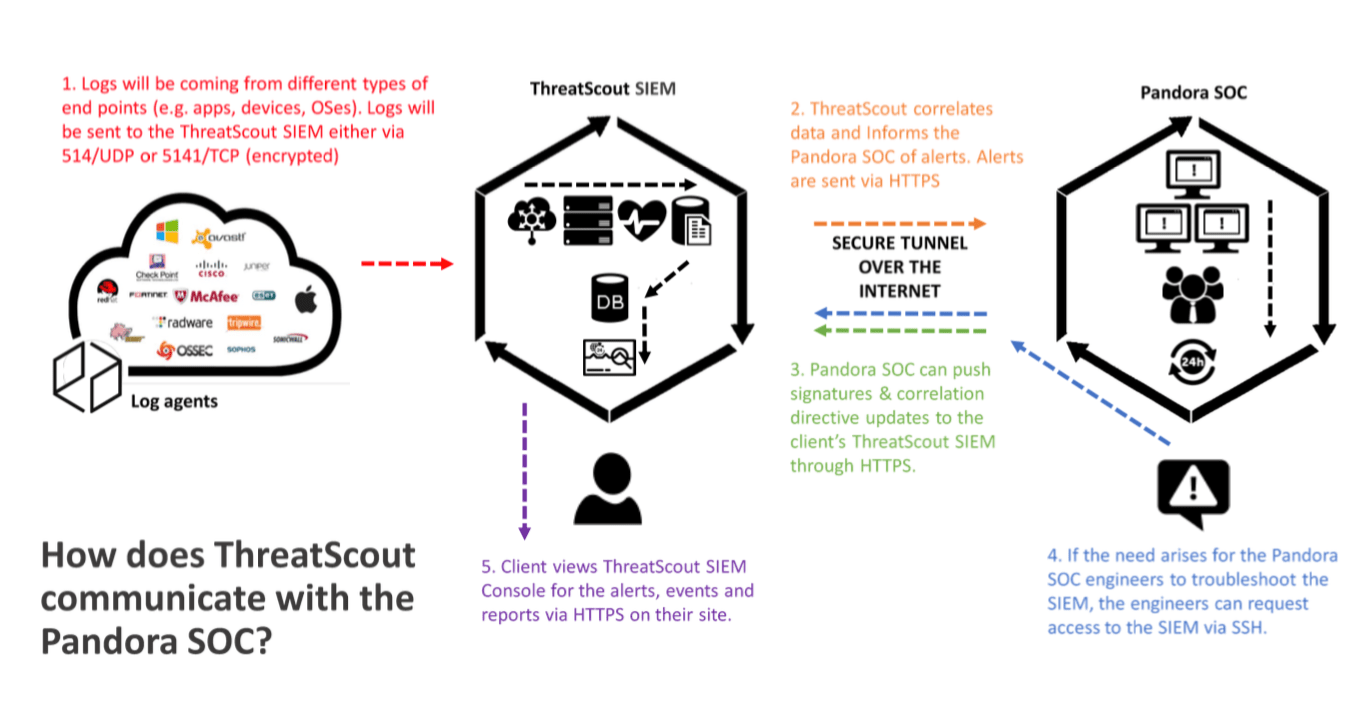
ThreatScout is an SIEM built by Pandora Labs that provides the capability to collect, correlate and store logs from multiple devices. With its next-generation correlation engine, it is capable of monitoring and detecting incidents from your network. ThreatScout also provides the required reports for compliance and custom reports for you.
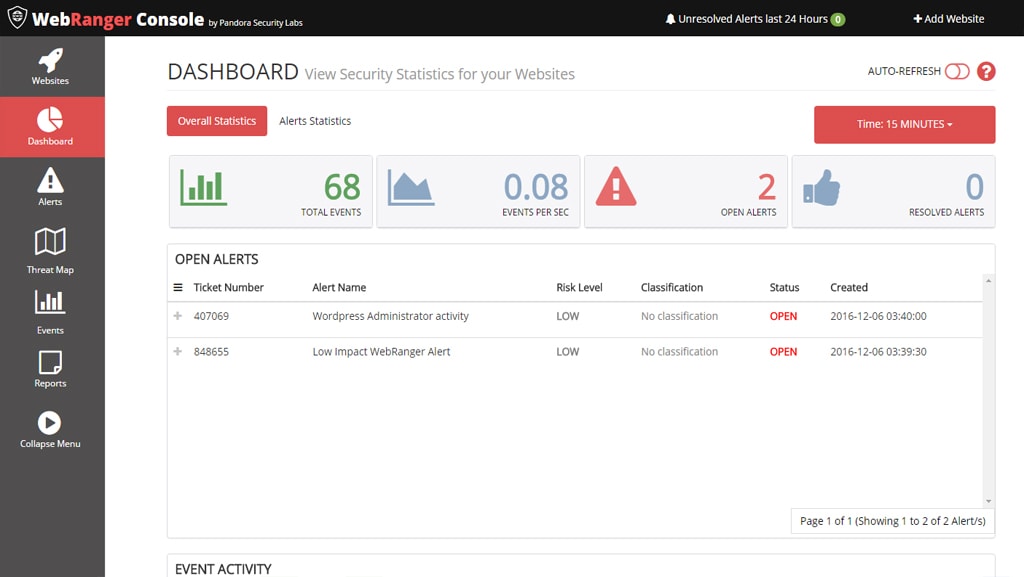
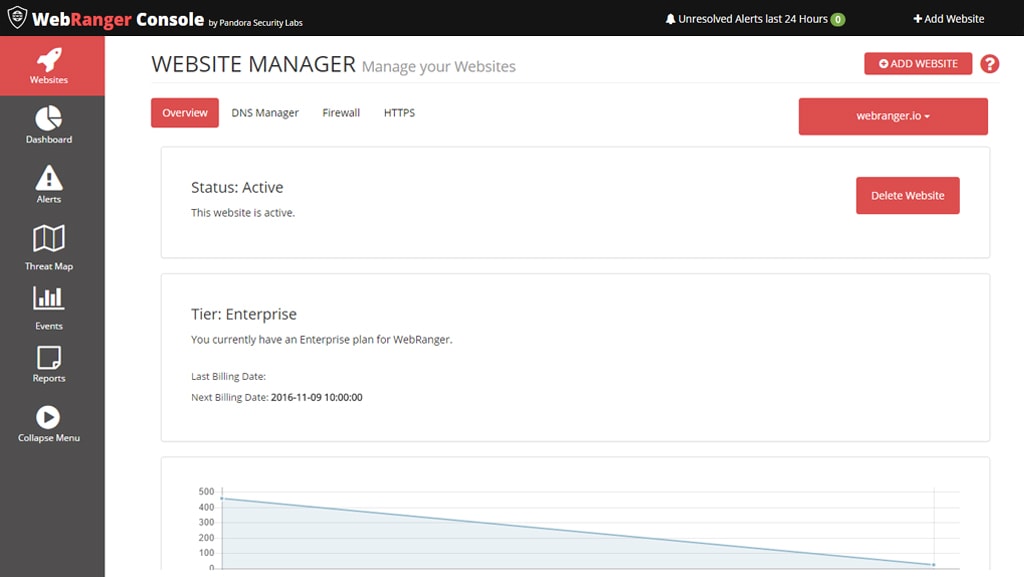
WebRanger is a web application firewall built by Pandora Labs that protects your website 24×7. WebRanger guarantees immediate notification by a team of expert responders while they investigate the cause of the attack, what it’s trying to attack and immediate resolve the attack – while it’s happening and before they can cause any damage.
RESEARCH & DEVELOPMENT
As our name explains, Pandora Security Labs’ soul and core is research and development. We provide the leading security solutions through cutting-edge research. We provide you with the most cost-effective security solutions needed and make sure that you are always at the leading and cutting edge. By our research and development, you’ll get the best advice and experience the greatest advantage.
PRINCIPLE OF TRUST
Our principle of partnership is what keeps us ahead among the rest. We are open to be your trusted partner for all your security solution needs, putting your interest at our top most priority. This also means fewer vendors to manage, easier to monitor performance, better service and lower total cost of ownership.
SCALABLE SERVICES
We have tailored our services so as to not be overwhelming to grasp, and at the same time, easy to augment with other existing security services. We have designed our services in such a way that you don’t have to spend additional retainer’s fee for something unpredictable (and in most cases, not justifiable), and they are available on demand.
1. Attackers attack your network & systems and applications
2. Client existing sensors identifies anomaly and sends data to ThreatScout
3. ThreatScout correlates data and informs the Pandora SOC of alerts
4. Pandora SOC determines if alert is a true alert and informs the client
5. Pandora SOC logs into client’s devices (if allowed) to block the traffic
6. True alerts are then communicated to the client either via phone or email
7. Client views ThreatScout Console for the alerts and attacks resolved
8. Attacks with same patterns are blocked